By Patrick Colbeck
Social media is filled with a mix of like-minded supporters, venom-spitting trolls, and authentically inquisitive minds. So when I received the following reply to one of my posts on Twitter, I decided to take a leap of faith by assuming that the one who issued the following reply fell into the latter category.
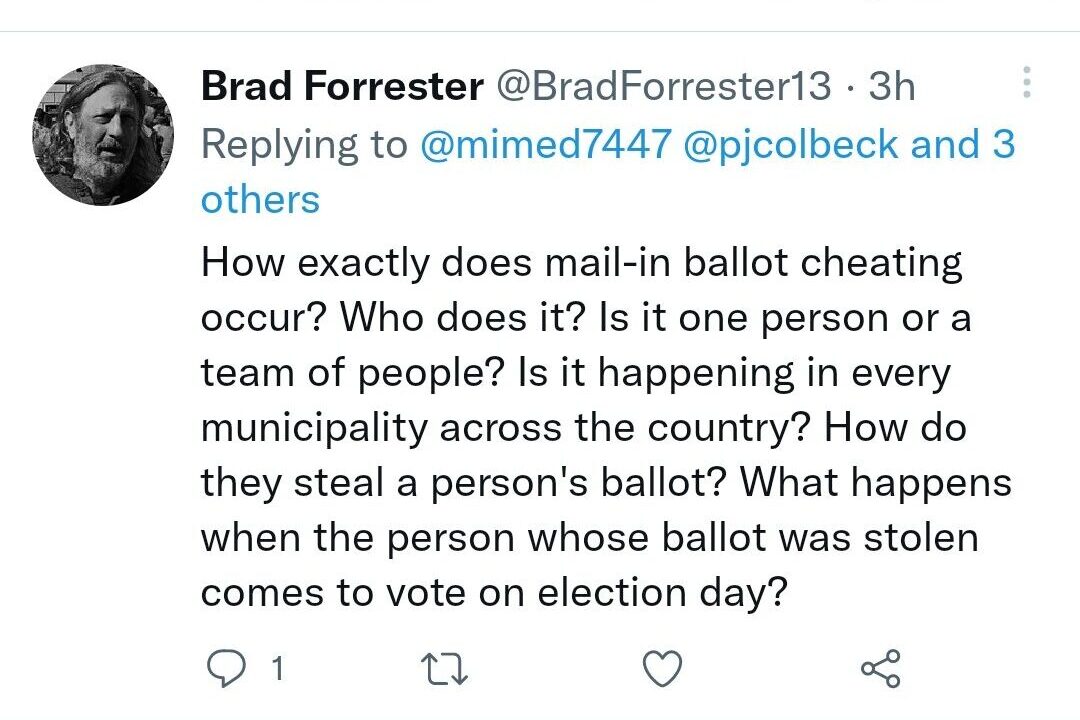
What follows is my attempt to respond to his inquiries without being subject to Twitter’s 280 character limit.
Mail-In Ballot Fraud Overview
Let’s start by addressing the overarching question, “How exactly does mail-in ballot cheating occur?”.
While there are many variations on the theme, the basic steps involved with mail-in ballot fraud are as follows:
- Inflate voter rolls in order to provide fake voters to which ballots can be allocated
- Send out absentee voter applications to everyone in the voter registration database and ensure that return to sender address is staffed by fraudsters who can flag voter associated with returned applications as “phantom voters” to which ballots can be allocated without mishap
- Remove or relax voter identity requirements
- Predict voter turnout…the more granular the prediction the better
- Calculate the number of ballots that need to be “stuffed” in order to ensure victory for your candidate
- Promote the use of satellite voting centers or other more discrete locations where fraudsters can pick up absentee ballots.
- Promote the use of unstaffed dropboxes where fraudsters can drop off their absentee ballots without risk of uncomfortable questions.
- Monitor election returns. If there are more voters than anticipated, inject late-night ballot drops in friendly jurisdictions to make up the difference.
- Update poll books to account for late-night ballot injections.
- Prevent any meaningful audit of the election record chain of custody.
Who Does It?
Is it one person or a team of people? The more centralized the management of our elections becomes, the fewer the number of people required to implement mail-in ballot fraud. In the wake of the passage of the federal HAVA act, states like Michigan who receive HAVA funds do so on the condition that they develop a centralized voter registration database.
All that is necessary to execute mail-in ballot fraud now is a single corrupt individual with access to the state voter registration database. With access to this database, they can change mailing addresses, identity verification parameters, and voter history. Such access would enable unwitting local clerks to mail absentee ballots to phantom voters residing at addresses where the fraudster could collect the ballots. With ballots in hand, the fraudster would then deposit them discretely at drop boxes in order to avoid any inadvertent tracking by the US Postal Service. When poll workers in absentee vote counting boards process the absentee ballots, they will use the data in the state voter registration database to verify the identity of the voter. If everything checks out in accordance with the identity verification guidelines in place, the ballot is tabulated.
Given enough lead time, all it takes is a single bad actor. In order to expedite matters, however, mail-in ballot fraud is likely executed by a compartmentalized group of individuals, some of which likely believe everything they are doing is perfectly legal. In Michigan, there is a well-established network of organizations with access to our centralized voter registration database with little to no public oversight. These organizations as enabled by the Michigan Secretary of State include Rock the Vote and ERIC.
Is it happening in every municipality across the country?
Evidence from canvassing efforts in my home state of Michigan suggests that it occurred in every county in the battleground state of Michigan. That does not mean that every clerk in every county is complicit with the fraud as those truly complicit with the fraud falsely assert. Local clerks rely upon voter identity information and election processes provided by the state. A good clerk could easily do everything by the book and still preside over a fraudulent election when mail-in ballots are involved.
How do they steal a person’s ballot?
Mail-in ballot fraud is generally much more sophisticated than taking a ballot away from a legitimate voter although that has been known to occur particularly in nursing homes and assisted living centers. In today’s information age, mail-in ballot fraud doesn’t require that they steal a person’s ballot. They simply have to borrow their identity. Once they have their identity, they can pick up an absentee ballot in the victim’s name (or fake person’s name) and drop it off discretely in a drop box. The fraudulent ballot then gets processed right along with all of the genuine absentee ballots cast by actual voters.
What happens when the person whose ballot was stolen comes to vote on election day?
Regrettably, there are affidavits testifying to such incidents occurring during the 2020 election in the City of Detroit. The risk of such an occurrence is diminished by the fact that the official voters assigned to fraudulent absentee ballots would already be flagged as “low propensity voters” (i.e. once in a blue moon voters). When this does happen, however, the person who comes in to vote in-person would feature a poll book entry denoting that they had already been issued an absentee ballot. When this happens, the poll worker would issue a provisional ballot to the voter. The provisional ballot is not supposed to be tabulated until the multiple ballot issue has been resolved. The poll book entry for the voter should then be flagged to denote that the voter intended to vote in person. If the clerk in that jurisdiction is committed to election integrity, they would ensure that any absentee ballots cast in that voter’s name would not be processed. Their ability to do so, however, is hampered by the fact that absentee ballots and in-person ballots for the same precinct are often processed at separate facilities with unique poll books. Any update to one poll book would not be reflected in the other poll book. The clerk, however, should serve as the bridge between the two poll books and ensure that two or more ballots are not counted for a single voter.
Why is mail-in ballot fraud such a concern?
Mr. Forrester didn’t ask this question, but I will. Mail-in ballot fraud is a concern because it is designed to avoid discovery. Poll watchers and poll challengers are allowed to observe the processing of ballots at in-person voting precincts and absentee vote counting boards. All 10 steps outlined in the mail-in ballot fraud overview feature little or no oversight by poll watchers and poll challengers. By the time those responsible for oversight review a ballot that is being processed, it is too late. The election is rigged long before the election day oversight operations.
In-person voting is a 1st person transaction. The voter shows up in person on election day. They verify their identity in person on election day. They insert their ballot into the voting system on election day. If there are any ballot errors, they are there to correct them in person. All of these activities can be monitored by poll watchers or poll challengers to ensure integrity.
Mail-in voting is inherently a 3rd party transaction. A third party mails a voter an absentee ballot. The voter deposits the absentee ballot into a drop box or mailbox managed by a third party. The identity of the voter associated with a ballot is then verified by a third party using data stored in a remote database. The ballot is then inserted into the voting system by a third party. If there are any ballot errors, a third party discerns the voter’s intent and allocates their votes accordingly. Most of these activities cannot be monitored by poll watchers or poll challengers to ensure integrity.
Due to its reliance on processes executed by third parties, mail-in ballot fraud is designed to avoid discovery, but it can be detected. The most effective way to discover mail-in ballot fraud is to canvass the voter rolls after the election. While states do have local canvassing boards that should theoretically perform this task, in practice, these boards simply serve as “rubber stamps” to the statements of votes provided by various jurisdictions. True canvassing of the voter rolls takes time and significant effort.
When election integrity groups have invested this time and effort, the results speak for themselves. Mail-in ballot fraud is evident and it is significant enough to change the outcome of our elections. For example, canvassing of the 2020 election results across eight counties in Michigan revealed voter anomaly rates of between 4% and 40% in a state where the Presidential election decided by a margin of 2.78%.
CONCLUSION
Our elections will never be truly secure until we clean up our voter rolls and eliminate mail-in voting.
RELATED INFORMATION
- Two Keys to Securing Our Elections
- Let’s Audit the MI Auditor General Report on Elections
- Michigan Mail-In Voting Issues
- Election Integrity Force Report 7: The Egregious State of Voter Registrations and the Canvass Results
- WI Ballot Trafficking Evidence
- 2000 Mules
- Election Fraud Evidence Palooza in New Book “The 2020 Coup: What Happened. What We Can Do
- Election Certification Overview


Did you happen to see James Jernigan’s latest video on YouTube?
You helped me a lot by posting this article and I love what I’m learning.
Great beat ! I would like to apprentice while you amend your web site, how could i subscribe for a blog site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear concept
I will right away grab your rss as I can’t find your email subscription link or e-newsletter service. Do you’ve any? Kindly let me know so that I could subscribe. Thanks.
Very interesting info!Perfect just what I was looking for!
The following time I learn a weblog, I hope that it doesnt disappoint me as much as this one. I mean, I do know it was my choice to read, but I truly thought youd have something interesting to say. All I hear is a bunch of whining about something that you can fix when you werent too busy searching for attention.
You are a very intelligent person!
Thanks for the guidelines you have discussed here. Another thing I would like to express is that laptop memory specifications generally increase along with other advances in the technological innovation. For instance, whenever new generations of processor chips are brought to the market, there is certainly usually a matching increase in the size demands of all laptop or computer memory plus hard drive room. This is because the application operated by these cpus will inevitably rise in power to make use of the new technological know-how.
Thanks for your article. My spouse and i have often noticed that many people are desperate to lose weight as they wish to look slim as well as attractive. However, they do not usually realize that there are more benefits to losing weight also. Doctors state that fat people suffer from a variety of conditions that can be instantly attributed to the excess weight. Fortunately that people who are overweight in addition to suffering from a variety of diseases can reduce the severity of their illnesses through losing weight. You are able to see a slow but notable improvement in health whenever even a bit of a amount of weight-loss is accomplished.
There are actually a variety of particulars like that to take into consideration. That could be a nice point to deliver up. I provide the thoughts above as common inspiration but clearly there are questions like the one you deliver up the place a very powerful factor will likely be working in sincere good faith. I don?t know if finest practices have emerged round issues like that, however I’m sure that your job is clearly identified as a good game. Each girls and boys feel the influence of just a moment’s pleasure, for the remainder of their lives.
I don’t even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you’re going to a famous blogger if you are not already 😉 Cheers!
Kopen een echt en geregistreerd rijbewijs van onze website zonder examens te schrijven of de oefentest te doen. alles wat we nodig hebben zijn uw gegevens en deze zouden binnen de komende acht dagen in het systeem worden geregistreerd. rijbewijs kopen belgië, rijbewijs kopen belgie, rijbewijs kopen in nederland, rijbewijs b belgie, rijbewijs kopen met registratie. https://rijbewijskopenbetrouwbaar.com/
I have been reading out many of your stories and i can claim nice stuff. I will make sure to bookmark your site.
Comprar carta de condução legalmente, Comprar carta de condução sem pré-pagamento, uma carteira de motorista registrada compre experiências, comprar experiências de carta de condução, Comprar carta de condução sem exame Colônia, Comprar carta de condução porto, Comprar carta de condução sem exame portugal, Comprar carta de condução em portugal, comprar carta de condução lisboa, comprar carta de condução portugal.
https://comprarcartadeconducaoportugal.com/
Comprare patente di guida reale e registrata sul nostro sito web senza sostenere alcun esame o fare la prova pratica. tutto ciò di cui abbiamo bisogno sono i tuoi dati e verranno registrati nel sistema entro i prossimi otto giorni. Le patenti di guida devono seguire la stessa procedura di registrazione di quelle rilasciate nelle autoscuole
https://patentecomprata.com
Acheter permis de conduire réel et enregistré sur notre site Web sans passer d’examens ni passer l’examen pratique. tout ce dont nous avons besoin, ce sont vos données et elles seront enregistrées dans le système dans les huit prochains jours. Les permis de conduire doivent passer par la même procédure d’enregistrement que ceux délivrés dans les auto-écoles.
https://acheterpermisconduireligne.com/
führerschein kaufen legal, führerschein kaufen ohne vorkasse, registrierten führerschein kaufen erfahrungen, führerschein kaufen erfahrungen, führerschein kaufen ohne prüfung Köln, führerschein kaufen österreich, führerschein kaufen ohne prüfung österreich, führerschein kaufen ohne prüfung österreich, führerschein kaufen in österreich, führerschein kaufen Frankfurt, führerschein kaufen schweiz. https://registriertenfuhrerschein.com/
These days of austerity as well as relative stress about running into debt, a lot of people balk up against the idea of employing a credit card in order to make purchase of merchandise or even pay for a vacation, preferring, instead just to rely on the particular tried and trusted procedure for making transaction – cash. However, in case you have the cash there to make the purchase fully, then, paradoxically, that’s the best time for you to use the cards for several factors.