By Patrick Colbeck
Georgia election officials had denied that their election equipment was connected to the internet. The truth? Not only were they connected. They were vulnerable. In fact, it took a “White Hat” hack to demonstrate they were vulnerable in the wake of assurances from former CISA Director Krebbs and the Election Infrastructure Government Coordinating Council (GCC) Executive Committee that this was the “most secure election in American history“.
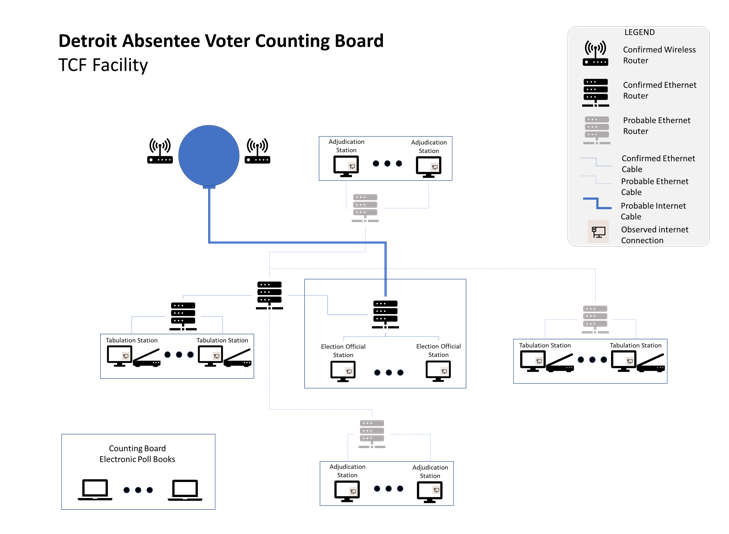
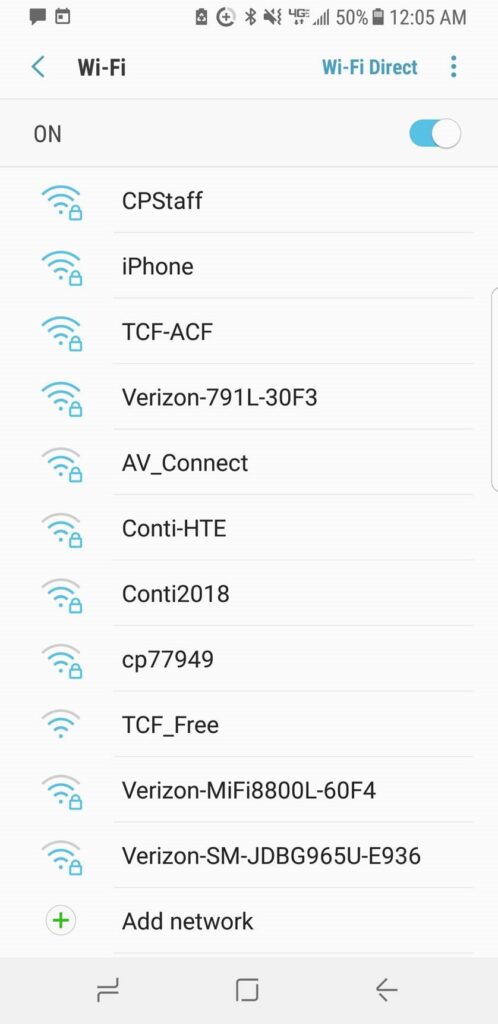
Michigan election officials have also denied that their election equipment was connected to the internet. I personally witnessed evidence to the contrary in Wayne County. Others witnessed evidence to the contrary in Antrim County.
Why did it take a “White Hat” hacker to demonstrate the vulnerability of our voting systems? Simply put, access to the electronic data has been denied. White hat hacking was the only option left in the eyes of many pursuing the truth. In fact, Antrim County was the ONLY jurisdiction in America to the best of my knowledge for which access to the electronic data regarding the election has been granted. Even then, the subsequent report was redacted at the request of Michigan Attorney General Dana Nessel’s administration. I have been told that the redacted portion of the report provided unequivocal evidence that several of the statements under oath by Dominion CEO John Poulos before a Michigan Senate Oversight committee were demonstrably false.
The fundamental question regarding election integrity, particularly the chain of custody pertaining to vote tally information, is this.
Why is access to the electronic election data being denied if there is nothing to hide?
There are literally thousands of affidavits attesting to election fraud across the country including the following personal observations that I made at the TCF Center in Detroit on election night.

Why aren’t prosecutors, Attorneys General, and the alphabet soup of federal agencies in charge of enforcing our laws pursuing subpoenas for this information?
Why wouldn’t this information being made public?
It should be noted that, in Michigan, the state legislature did issue a subpoena for the City of Detroit that included a request for electronic election information on December 15. What deadline did they give for the receipt of this information? It is due on January 12, 2021 which is conveniently AFTER the critical January 6, 2021 Electoral College Joint Session in DC.


Mr. Colbeck,
It is important to point out that the Michigan Secretary of State website NOW acknowledges that some machines were connected to the internet, but claims this occurs only AFTER all counting has finished. Damage control?
“…The machines are not connected to the internet until all counting is finished and copies of the tally have been printed. Then some jurisdictions may connect a machine to send UNOFFICIAL results to the county clerk, while a copy of the paper tally is also driven to the county clerk…”
Conveniently, the note is a bit light on details including a list of which precincts or counting boards are affected. It also does not explain how MCL 168.795(2) is satisfied by machines with remote reporting capability, let alone for ‘local network’ systems like the one at the TCF Center where operators of the ‘Results Tally and Reporting’ computers have access to real-time results from multiple tabulators.
“…Electronic tabulating equipment that counts votes at the precinct before the close of the polls must provide a method for rendering the equipment inoperable if vote totals are revealed before the close of the polls…”
I am sure there are audit logs recorded by the individual tabulators, ‘modems’, and ‘Results Tally and Reporting’ computers that prove no voting results information was available to any system operator “until all counting is finished and copies of the tally have been printed”. If only these logs were voluntarily and immediately made available for verification. It would also be nice if the raw source of the ‘official’ results (i.e. time-stamped tabulator tape print-outs) were made available for all to observe (i.e. posted to the internet) on election night.
I would also point out that the Georgia Secretary of State website still claims there is no internet connection to their voting equipment in their FAQ pages:
“…Q: How is the new system secured?
The D-Suite system will enable Georgia to defend against cyber threats and deliver reliable election results which can be audited using paper ballots.
Like the existing voting machines, the new machines do not connect to the Internet, which limits cyber security risks. They also create an auditable paper ballot, with other enhanced review capabilities for the public…”
This conflicts with public statements from Georgia Election Officials from earlier this year:
https://www.govtech.com/security/Georgia-Bolsters-Election-Security-with-New-Voting-System.html
“…The voting system includes a wireless connection to the internet, used in counties when voter registration information is loaded onto tablets. The internet access point is only turned on for a couple of minutes, information is encrypted, and information can be exchanged with specifically identified tablets…”
God Bless Michigan
God Bless America
Respectfully,
Lou
In one of the many hearings – not sure in which one – a woman working in a poling station said she had a software issue with the voting software system. She called and said that in a few minutes the issue was solved via remote (this means that they had access to her computer and presumably to all the system). This is done in many ways, one way is through a commercial VNC which needs open [standard] ports, I’ve had many servers and if the firewall(s) are properly set, when you look at the access, error and security warning log files it is amazing to see how many IPs try to enter/access your machine every hour through ope ports (like doors). Once a hacker is inside 1 machine and if it is interconnected via cable or WiFi then whoever is inside can have a field day: retrieve, change, erase, etc. – it seems that when expert techies access these machines under some subpoena or whatever to analyze, logs have been conveniently erased or “lost” – I’m not a lawyer or expert on hacking issues, but I think this is a crime and whoever erased or is responsible should be held accountable and/or give a valid explanation, if there is one which I doubt.
Mr. Colbeck, as an engineer and clear thinker willing to go against institutional narratives and bring solid information directly to readers, you have great value to the cause of truth and justice in public policy. Please don’t tarnish your reputation by giving people like “Jovan Pulitzer” a platform. A.k.a. Jovan Philyaw, “QR Code inventor” and lead historian for early Roman exploration of our continent – “single most important discovery” ever for America. There is also a need to clarify the 68% figure in the Antrim County Forensic study – log alert rate, not erroneous result rate.
Where can I get a copy of the 1000+ pages of forensic evidence discussed by Mary Fanning? I would like to construct some graphs and statistical analysis with the data.